How Can IoT Solution Providers Build a Secure IoT System at Different levels?
 Published: Apr 25, 2023
Iot
Share:
Published: Apr 25, 2023
Iot
Share:
The Internet of Things (IoT) has been attracting a lot of attention in the industry for its security due to many issues, such as various entrances and different communication standards. So, how can IoT solution providers build secure IoT systems at different levels? Recently, Mike Dow, senior product manager of IoT security at Silicon Labs, shared his insights with Electronic Business Council (ESMC).
IoT Security, Silicon Labs
As a Senior product anager, Mike Dow said, In fact, IoT security is riskier, more threatening and more serious than Internet security - IoT security risks threaten not only users' personal privacy and property security but also the security of critical information infrastructure and Its importance is evident.
According to the classification, the IoT security architecture can be divided into: perception layer security: which focuses on strengthening the security control of the confidentiality of the sensor network, node authentication and intrusion detection, security protection in the layers of information transmission links, perception layer security technology structure is more complex, in order to ensure the security protection strength at the same time need to ensure that the IoT device computing capacity, communication capacity and storage capacity is not affected.
Network Layer Security
Used to ensure communication security in the communication layer for high-intensity processing of data packets to provide data source address verification, connectionless data integrity, data confidentiality and limited service flow encryption and other security services.
Application Layer Security
The design focuses on improving the security and reliability of massive data information processing and business control policies and securing various types of services and business support platforms. Before we get started, let's introduce Mike Dow, who has spent 25 years in the semiconductor industry working for Motorola, Freescale, NXP and Silicon Labs. He is licensed as a Professional Engineer in the State of Texas, USA. He has extensive experience in promoting and participating in wireless standards organizations such as IEEE and ISA, as well as helping to found the Wireless Industry Technology Consortium (WiTECK), of which he served as Chairman and President from 2007 to 2009. Over the past 11 years, he has held positions in business development, new product development and marketing, focusing on verticals such as security, connectivity, IoT, industrial IoT, point-of-sale terminals and smart energy.
Here's a Conversation with Mike Dow on "IoT Security" from Electronic Commerce International
Mike Dow: IoT end devices that use Linux-based microprocessors (MPUs) are easy targets, but wireless interfaces such as Bluetooth LE, Wi-Fi, Zigbee, etc., are also starting to become the most vulnerable to hackers. /MPU IoT devices as targets for malware injection.
ESMC: Are existing trusted computing processing chips and encryption algorithms sufficient to create secure IoT systems?
Mike Dow: Suppose the trusted computing processing chip refers to a TPM chip (i.e., a secure chip that meets the TPM Trusted Platform Module standard). If this is the case, then the answer is no. Only the TPM and the device's own encryption are not enough to secure an IoT system. Now, you need to ensure that the code running on the device every time it resets is authenticated. This requires a multi-stage secure boot process with a trust anchor located in the read-only memory (ROM) code. Another hard requirement is to have some basic local attack protection against impulse and side-channel attacks, which typically bypass debug locks or obtain keys.
ESMC: What role can today's IoT operating systems (e.g., AliOS, China Mobile OneOS, Huawei LiteOS, Google Android Things) play in creating secure IoT systems?
Mike Dow: Operating systems can play a role in helping to distinguish security-related code from non-security-related code. This provides benefits for protection against remote attacks and also supports the segmentation of code bases that may require additional security hardening and/or security certification.
ESMC: Is Silicon Labs' Secure Vault IoT security software an IoT OS? Mike Dow: Secure Vault is not an IoT OS. The base firmware in our Secure Vault security subsystem consists of ROM code and firmware that is strictly controlled, signed, and verified by Silicon Labs (and only by Silicon Labs). Even within Silicon Labs, we strictly control access to this code base as it is the Root of Trust for all other security features in the chip. However, we realize that security threats evolve over time, so our Root of Trust must also evolve over the lifecycle of deployed products. Therefore, we provide a secure over-the-air (OTA) method to transfer encrypted updates to our Root of Trust firmware and then install and securely launch those updates.
IoT security has been a concern in the industry since its inception, and the outbreak of 5G popularity is pushing IoT development into a new dimension. IoT security issues will become more complex and multi-faceted and will certainly rise from personal property and information security hazards to those involving personal safety, such as connected cars and autonomous driving, which requires upstream companies to provide security solutions from multiple levels, such as hardware and software.
As a company specializing in the development and design of analogue circuits and mixed-signal ICs, Silicon Labs has grown into a world-renowned one-stop provider of smart IoT solutions over the past 25 years since its establishment. At the "2021 International AIoT International Eco-Development Conference" to be hosted by ASPENCORE in Shenzhen Kexing Science Park on June 10, 2021, Mr Wei Zhou, General Manager of Silicon Labs China, will also deliver a speech titled "Smart and Secure Wireless Connectivity At the conference, Mr Wei Zhou, General Manager of Silicon Labs China, will also deliver a speech titled "Smart and Secure Wireless Connectivity Solutions", where more detailed solutions for secure IoT connectivity will be presented. At the same time, Silicon Labs also has a booth at the conference, which will showcase the physical reference design solutions for Bluetooth wireless connectivity, facilitating on-site technical exchanges and solution tours.
Recommend Products
Related Solutions
-
NXP Introduces High-Power Wireless Charg...
NXP Semiconductors announced the first high-power wireless charging solution for notebooks and 2-in-...
Apr 28, 2023 Consumer Electronics -

Multifunctional Street Light Automatic C...
The street light automatic controller is suitable for the automatic control of street lights in resi...
Apr 26, 2023 Consumer Electronics -

How Can IoT Solution Providers Build a S...
The Internet of Things (IoT) has been attracting a lot of attention in the industry for its security...
Apr 25, 2023 Consumer Electronics -
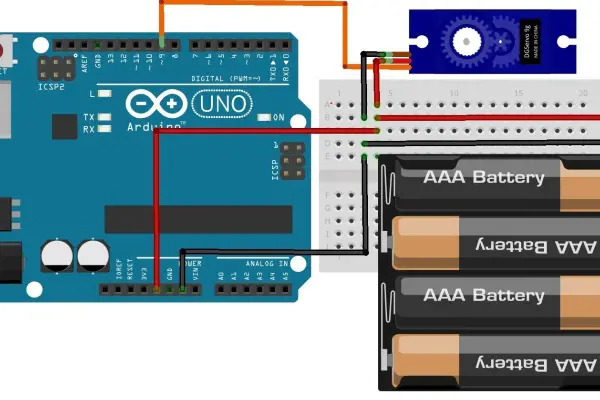
ADI Proposes a Solution for Servo Motor ...
For motor control solutions, ADI offers a comprehensive portfolio of products, including analog-to-d...
Apr 25, 2023 Consumer Electronics -

IoT Transforms and Adds Value to Consume...
The Internet of Things (IoT) is taking consumer electronics to another level and could lead to the n...
Apr 26, 2023 Consumer Electronics -

Texas Instruments Programmable Logic and...
Programmable logic controllers (PLCs) and programmable automation controllers (PACs) process and con...
Apr 26, 2023 Consumer Electronics

 Update Time: Apr 25, 2023 Consumer Electronics
Update Time: Apr 25, 2023 Consumer Electronics